Canvas Cyberattack Exposes Millions of Student Records, Disrupts Finals
Breach of Canvas LMS exposes personal data of ~30 million users, disrupts finals, and raises phishing risks. See impact and mitigation steps.
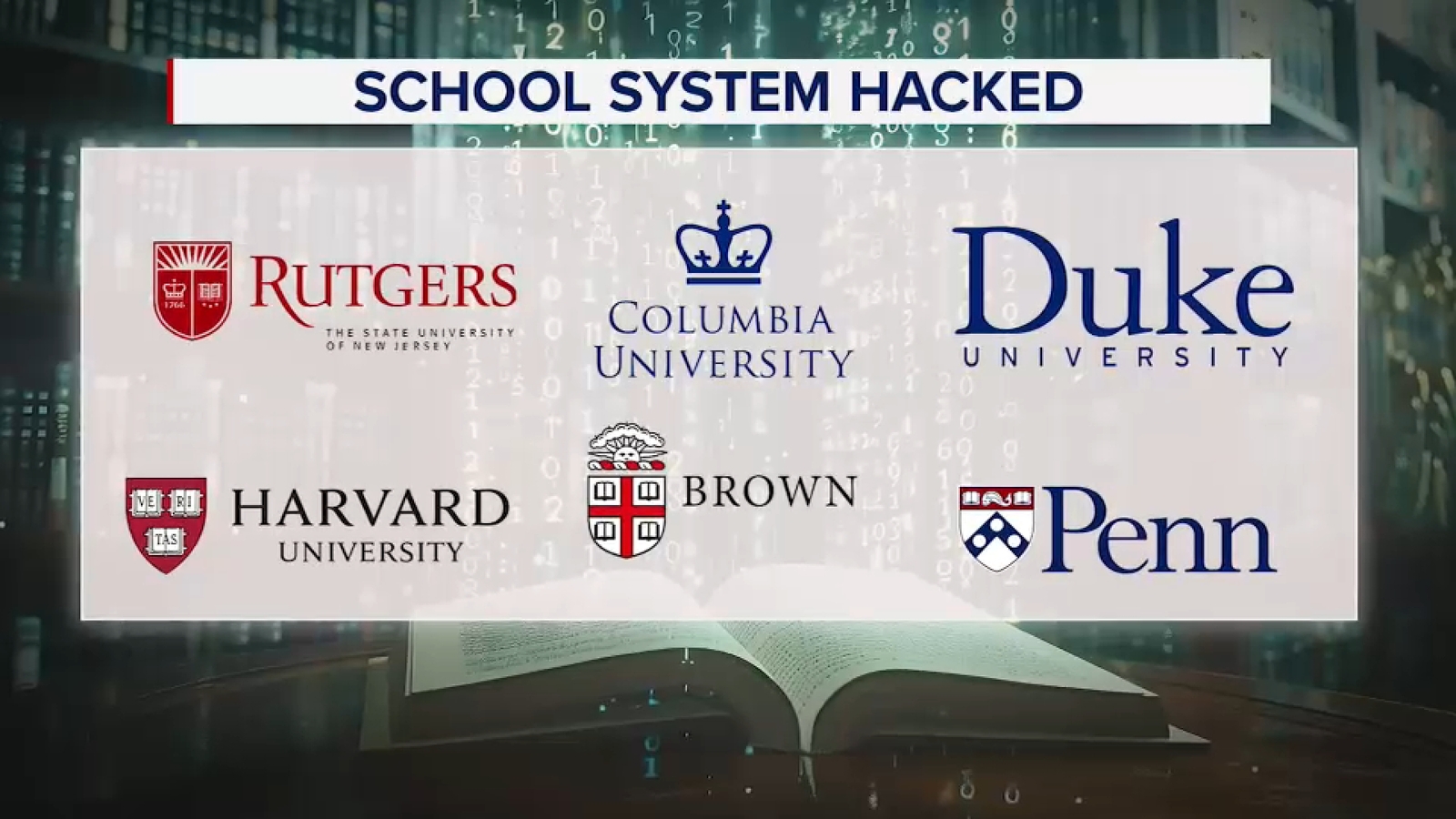
TL;DR: On Thursday night a criminal threat actor disrupted Canvas, the learning management system used by about 30 million active users, and claimed to have stolen names, emails, phone numbers, student IDs and internal messages. The outage delayed final projects and exams at Columbia, Rutgers, Princeton and other institutions, while the attacker group ShinyHunters demanded a ransom to prevent data release.
Context: Instructure, Canvas’ parent company, described the incident as a cybersecurity attack perpetrated by a criminal threat actor. ShinyHunters publicly claimed responsibility and threatened to leak the data unless paid. The disruption began Thursday evening and persisted into Friday, prompting schools to suspend Canvas access, clear browser caches, and postpone finals while they assessed safety. Student Barry Battle said the outage caused him to miss deadlines on final projects, calling it a major inconvenience.
Key Facts: Approximately 30 million active users rely on Canvas across K‑12 and higher education. The compromised data set includes personal identifiers and internal communications, though passwords were not reportedly stolen. Cybersecurity expert Rachel Tobac warned that the stolen information could be used to craft convincing phishing messages impersonating professors to lure students into clicking malicious links.
What It Means: The breach highlights how attackers exploit widely used ed‑tech platforms to harvest data for secondary social‑engineering campaigns. Institutions must treat the incident as a data‑loss event, not merely an availability issue, and anticipate follow‑up phishing attempts targeting students and staff.
Mitigations: Apply the latest Instructure security patches and review Canvas instance configurations for excessive permissions. Enable multi‑factor authentication for all admin and user accounts. Monitor logs for credential‑harvesting activity (MITRE ATT&CK T1078) and phishing lure delivery (T1566). Deploy email gateway rules that flag messages containing student‑specific details from the breach. Educate users to verify unexpected requests via separate channels and to avoid password reuse across services.
What to watch next: Watch for any public release of the claimed data, an increase in phishing campaigns referencing Canvas or university coursework, and further statements from Instructure regarding forensic findings and remediation timelines.
Continue reading
More in this thread
Second Canvas Breach Exposes Data of Nearly 300 Million Users, Triggers Test Cancellations
Peter Olaleru
Canvas Data Breach Exposes 9,000 Universities Worldwide, ShinyHunters Allegedly Steal 3.65TB
Peter Olaleru
Second Canvas breach in eight days exposes data of nearly 300 million users
Peter Olaleru
Conversation
Reader notes
Loading comments...