Second Canvas breach in eight days exposes data of nearly 300 million users
Canvas faced its second breach in eight days, exposing nearly 300 million users' data and disrupting finals at Penn State. Learn what happened and what defenders should do.
TL;DR: Canvas suffered a second breach in eight days, exposing data of nearly 300 million users and forcing Penn State to cancel finals.
On May 7, Instructure confirmed that attackers again infiltrated its Canvas learning‑management system, just days after a similar incident on April 29. The threat actors exploited a vulnerability in the Free‑For‑Teacher portal, gaining unauthorized access to user accounts and altering pages seen by some students and teachers.
The breach exposed sensitive information of almost 300 million Canvas users, including names, email addresses, student IDs, and personal messages. No additional data was taken during the May 7 incident, but the unauthorized modifications disrupted service for thousands of institutions during final‑exam week. Penn State responded by canceling all tests scheduled for Thursday night and all day Friday, and many other schools offered grace periods for missed assignments.
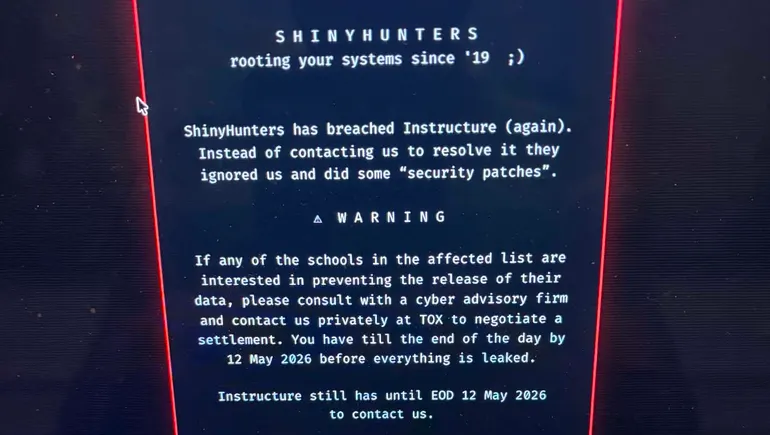
Technical analysis indicates the activity aligns with MITRE ATT&CK techniques T1078 (Valid Accounts) and T1190 (Exploit Public‑Facing Application). The group ShinyHunters left messages demanding negotiation to prevent further data leaks, echoing tactics seen in prior education‑sector attacks.
What It Means: Defenders should immediately disable Free‑For‑Teacher accounts until patches are applied, enforce multi‑factor authentication on all administrative portals, and review logs for anomalous page‑change events. Implement detection rules for MITRE technique T1078.003 (Cloud Accounts) and T1190, and apply any advisories released by Instructure for the Free‑For‑Teacher vulnerability. Institutions must also communicate clear incident‑response timelines to students and faculty to maintain trust.
Watch for any follow‑up extortion attempts, potential public release of the alleged data set, and Instructure’s post‑mortem report detailing the exact vulnerability and remediation steps.
Continue reading
More in this thread
Sequoia Says AGI Arrived as AI‑Powered Attacks Outpace Human Defenses
Peter Olaleru
Instructure Disables Free-For-Teacher Canvas Accounts After Hack Exposes Student Data
Peter Olaleru
Instructure Halts Free‑For‑Teacher Canvas Accounts After Hack Exposes Millions
Peter Olaleru
Conversation
Reader notes
Loading comments...