Second Canvas Breach Exposes Data of Nearly 300 Million Users, Triggers Test Cancellations
Instructure's Canvas LMS suffered a repeat breach, leaking data of nearly 300 million users and causing Penn State to cancel exams.
Second Canvas Breach Exposes Data of Nearly 300 Million Users, Triggers Test Cancellations
TL;DR
Instructure confirmed a second Canvas breach within eight days, exposing personal data of nearly 300 million users and prompting Penn State to cancel scheduled tests.
Context Instructure’s Canvas learning management system, used by thousands of colleges, suffered two separate intrusions—first reported on May 1 and a follow‑up on May 7. Both attacks targeted the platform’s Free‑For‑Teacher accounts, a feature that allows educators to create courses without a paid subscription. The timing coincided with final‑exam week, amplifying operational impact.
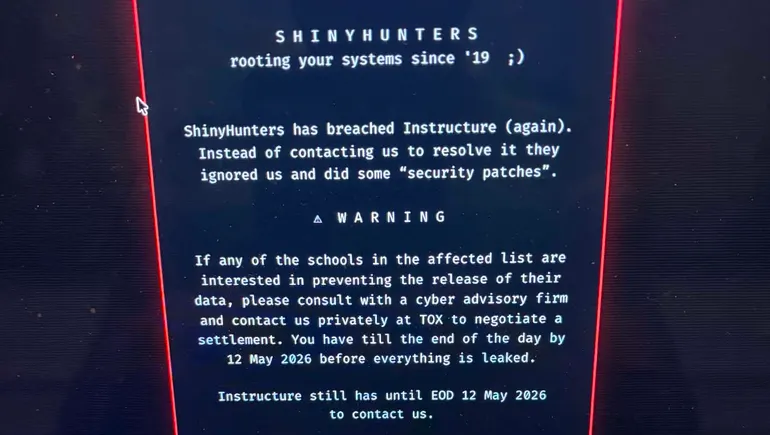
Key Facts - The May 7 intrusion allowed an unauthorized actor to modify login pages and extract data from accounts. No additional data beyond the first breach was reported, but the changes disrupted access for students and faculty. - Elizabeth Laird of the Center for Democracy & Technology said the breach exposed private messages and other personal information for almost 300 million Canvas users. - Universities across the country reported outages; Penn State cancelled all tests scheduled for Thursday night and Friday, citing the Canvas outage as the cause. - Threat‑actor group ShinyHunters posted messages on compromised Canvas instances, listing affected institutions and offering a settlement deadline of May 12 to prevent further data release. - Instructure responded by temporarily disabling Free‑For‑Teacher accounts and restoring the service by Friday, stating the platform is now safe to use.
What It Means The repeat breach underscores the vulnerability of education‑technology platforms that store massive amounts of student and staff data. With funding cuts to federal education‑technology support, many institutions lack robust security resources, creating an asymmetry where users cannot audit or control data protection. The incident also highlights the operational risk of relying on a single SaaS provider during critical academic periods.
Mitigations – What Defenders Should Do 1. Disable or restrict Free‑For‑Teacher accounts until a thorough security review confirms they are patched. 2. Apply vendor patches promptly; monitor Instructure advisories for CVE identifiers related to authentication bypass or web‑application flaws. 3. Enforce multi‑factor authentication (MFA) for all faculty and staff logins to reduce credential‑theft risk. 4. Deploy web‑application firewalls (WAF) with signatures for known MITRE ATT&CK techniques such as T1190 (Exploit Public‑Facing Application) and T1078 (Valid Accounts). 5. Conduct regular log reviews for anomalous page‑modification events and unauthorized access attempts. 6. Develop an incident‑response playbook that includes rapid communication with students, fallback assessment methods, and coordination with the vendor. 7. Consider data‑loss‑prevention tools to monitor outbound traffic for large exports of personal information.
Looking Ahead Watch for any settlement negotiations with ShinyHunters and for Instructure’s forthcoming security roadmap, which may include stricter account controls and expanded monitoring capabilities.
Continue reading
More in this thread
Sequoia Says AGI Arrived as AI‑Powered Attacks Outpace Human Defenses
Peter Olaleru
Instructure Disables Free-For-Teacher Canvas Accounts After Hack Exposes Student Data
Peter Olaleru
Instructure Halts Free‑For‑Teacher Canvas Accounts After Hack Exposes Millions
Peter Olaleru
Conversation
Reader notes
Loading comments...