Canvas Breach Exposes Millions of Student Data as ShinyHunters Demands Ransom
Canvas outage affects 30 million users; ShinyHunters claims data theft and ransom. Impact, timeline, and defender actions explained.
TL;DR
A cyberattack on Canvas forced the platform offline, disrupted finals, and exposed personal information of about 30 million active users. The hacking group ShinyHunters claims responsibility, threatens to leak data, and demands a ransom.
Context
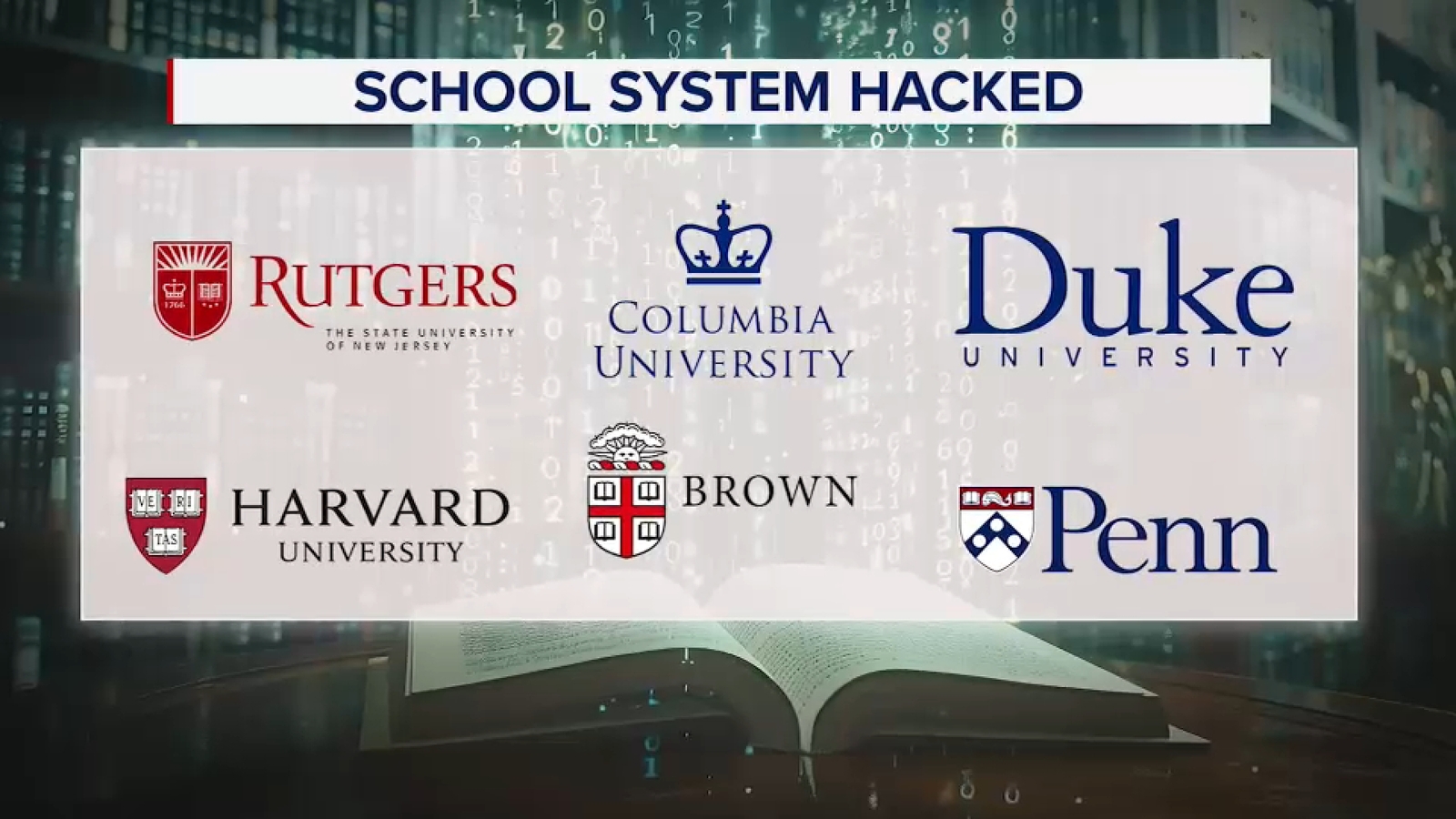
Canvas, a widely used learning management system, went dark on Thursday night after its parent company reported a "cybersecurity incident." The outage affected thousands of K‑12 and higher‑education institutions, with some schools postponing final exams. Students reported being unable to submit projects or access study materials, adding stress during exam week.
Key Facts
- Canvas reports roughly 30 million active users worldwide. - Student Barry Battle said the disruption prevented him from turning in final projects on time. - ShinyHunters announced responsibility for the breach and threatened to release stolen data unless a ransom was paid. - The exposed information may include names, email addresses, phone numbers, student ID numbers, and internal messages. - No evidence has been released that passwords were compromised, but attackers could use the harvested details for targeted phishing.
What It Means
The incident highlights how attackers target education technology to harvest personal data for extortion or social‑engineering campaigns. Even without password theft, the stolen profile data enables convincing impersonation of faculty or peers, increasing the risk of credential harvesting and further intrusions. Institutions relying on Canvas must treat the breach as a live threat to both privacy and operational continuity.
Mitigations
- Enforce multi‑factor authentication for all Canvas admin and user accounts. - Review and restrict third‑party integrations that could serve as entry points. - Monitor login logs for impossible travel or brute‑force patterns (MITRE ATT&CK T1110). - Deploy detection rules for unusual data exfiltration over HTTPS (T1041). - Ensure all Canvas instances are patched to the latest version; consult the vendor’s security advisory for any known CVEs. - Educate users about phishing tactics that leverage personal details from the breach. - Maintain offline, encrypted backups of critical course data to reduce ransom leverage.
Watch for any follow‑up ransom notes, potential data leaks on underground forums, and forensic updates from Canvas regarding the attack vector and scope.
Continue reading
More in this thread
Second Canvas Breach Exposes Data of Nearly 300 Million Users, Triggers Test Cancellations
Peter Olaleru
Canvas Data Breach Exposes 9,000 Universities Worldwide, ShinyHunters Allegedly Steal 3.65TB
Peter Olaleru
Second Canvas breach in eight days exposes data of nearly 300 million users
Peter Olaleru
Conversation
Reader notes
Loading comments...