Columbia Students Navigate Exam Stress as Canvas Data Breach Exposes Personal Data
Canvas breach may have leaked names, emails and student IDs, increasing phishing risk for Columbia students during finals. Mitigations and outlook.
A May 2 cybersecurity incident at Canvas’ parent company may have leaked names, emails and student IDs, raising phishing risks during finals.
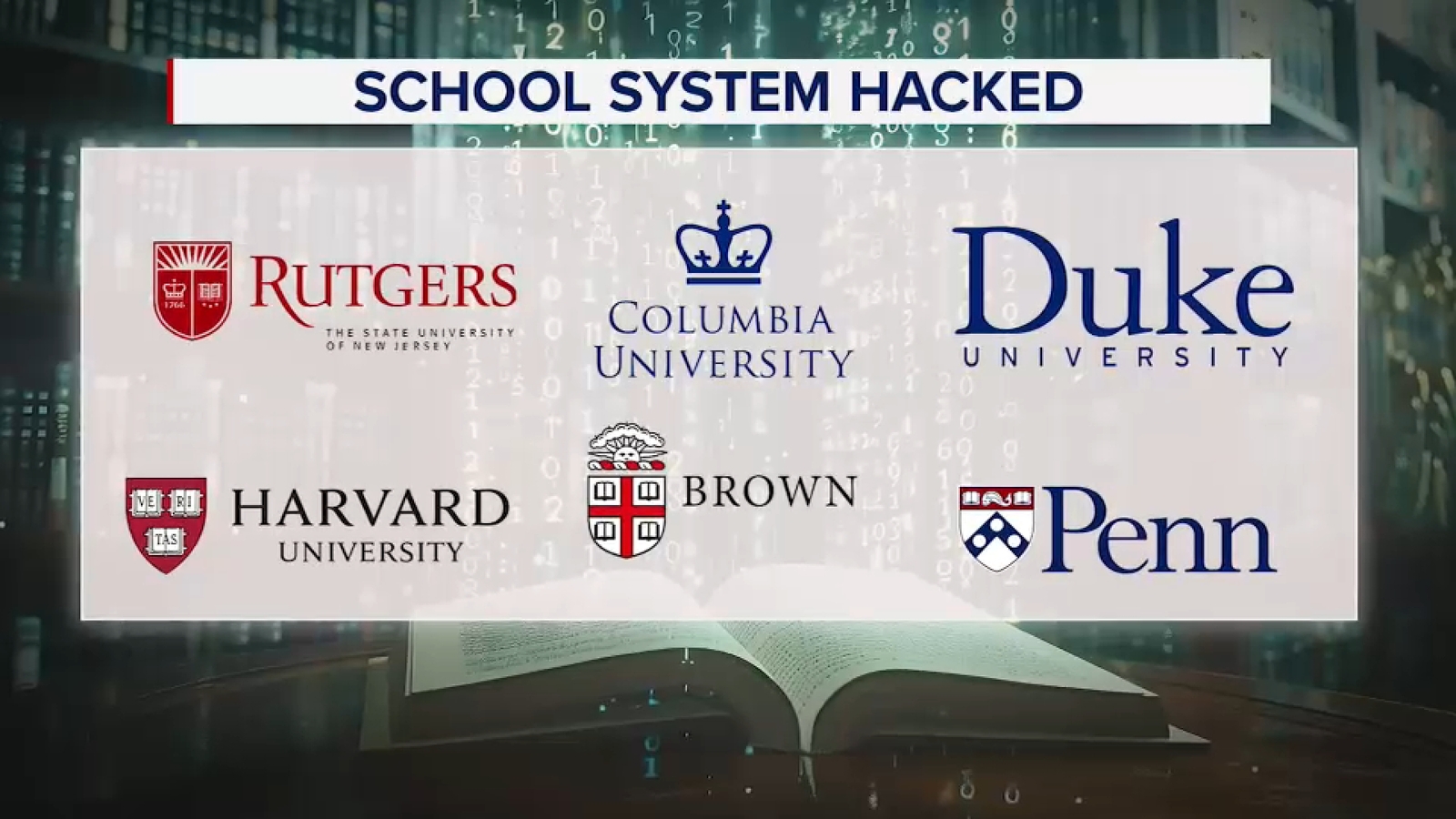
Canvas, the learning management system used by Columbia University and many other colleges, went offline after its parent company, Infrastructure, disclosed a cybersecurity incident on May 2. The outage blocked students from accessing lecture slides, assignments and messages just as final exams approach.
According to Infrastructure, a criminal threat actor carried out the attack. Cybersecurity expert Rachel Tobac said the breach likely exposed personal information including names, email addresses, phone numbers, student ID numbers and internal messages. While passwords were not disclosed, the stolen data could enable highly convincing phishing messages that appear to come from professors or course staff.
The timing compounds stress for students juggling coursework and exam preparation. Senior Zion James noted that his science and psychology slides reside exclusively on Canvas, making the outage a direct obstacle to studying. Sophomore Jerry Yan echoed the concern, saying all his lecture materials are stored in the platform and he needs immediate access.
What It Means
Attackers can use the harvested details to craft spear‑phishing emails that reference specific courses or assignments, increasing the likelihood of credential theft or malware delivery. Defenders should treat any unexpected message requesting urgent action as suspicious, even if it appears to come from a known instructor.
Mitigations include: - Enforcing multi‑factor authentication on all university accounts. - Blocking emails with spoofed sender domains using DMARC, SPF and DKIM policies. - Deploying anti‑phishing gateways that detect look‑alike URLs and urgent language. - Educating students and staff to verify unexpected requests through a separate channel (e.g., a known phone number or official portal). - Monitoring for MITRE ATT&CK technique T1566.001 (spearphishing attachment) and T1078 (valid accounts) in logs.
Organizations should also review Infrastructure’s security advisory for any released patches or configuration hardening guides related to the Canvas platform.
What to watch next: Whether threat actors follow up with targeted phishing campaigns exploiting the leaked student data, and how quickly Columbia and other institutions restore full Canvas access while implementing the above defenses.
Continue reading
More in this thread
Conversation
Reader notes
Loading comments...