Canvas breach leaks student IDs and emails across U.S. schools
A criminal group accessed Canvas, exposing student IDs, emails and messages at schools nationwide. Learn the impact and recommended mitigations.
*TL;DR: A criminal group known as Shiny Hunters compromised the Canvas learning platform, exposing student IDs, email addresses and internal messages for schools and universities across the United States.
Context In late April, security logs from Instructure, the company behind Canvas, showed unauthorized access to the platform’s backend. The breach was first reported publicly on May 7 after the University of Virginia (UVA) confirmed that a threat actor had extracted data from its Canvas accounts. UVA’s data‑science professor Daniel Graham warned that the shared nature of Canvas means any breach can affect every institution that relies on the service.
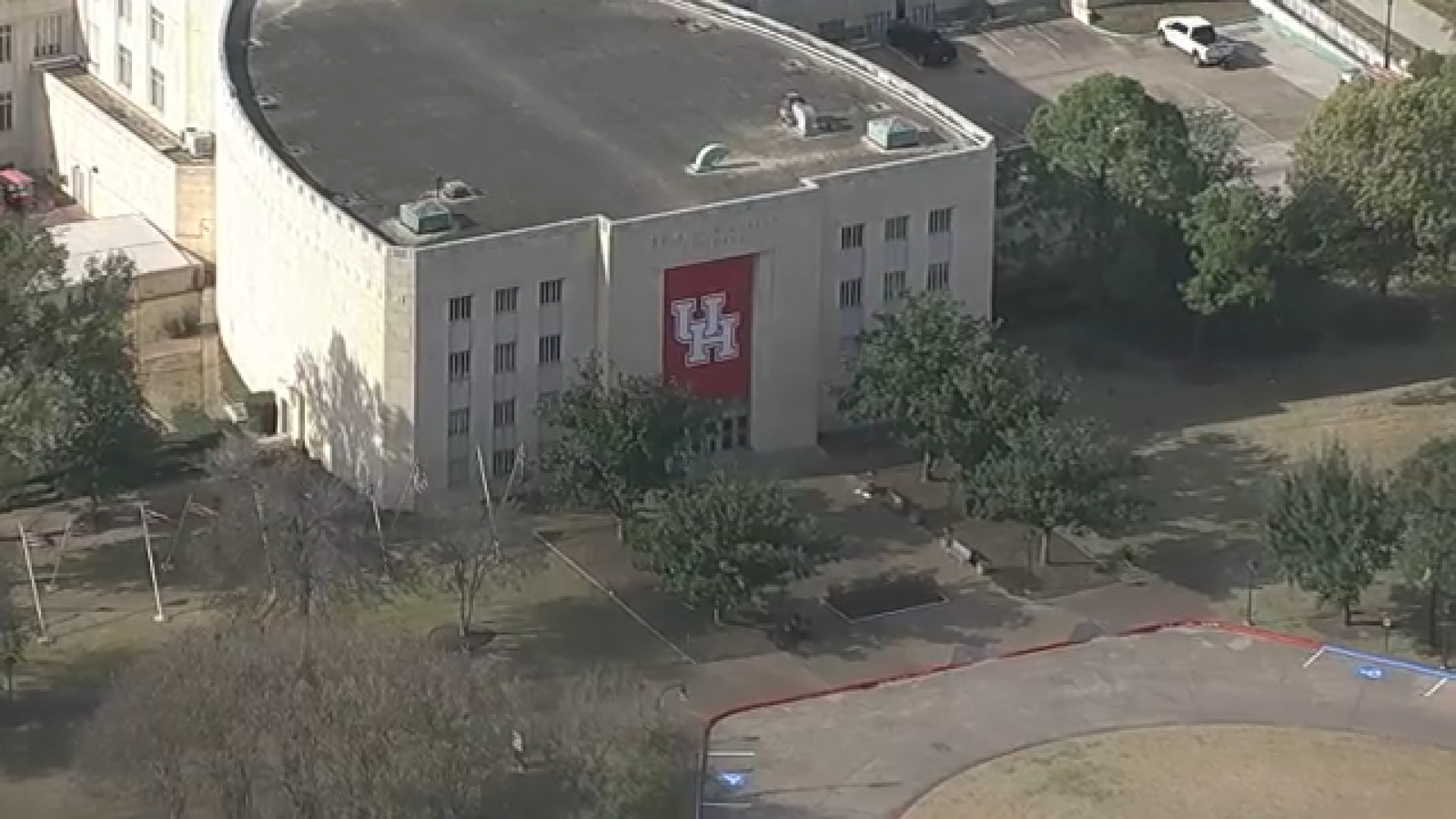
Key Facts - The attack vector appears to be credential theft combined with exploitation of a misconfigured API endpoint, allowing the group to enumerate accounts and download stored data. No public CVE (Common Vulnerabilities and Exposures) has been assigned yet, but the technique aligns with MITRE ATT&CK T1078 (Valid Accounts) and T1041 (Exfiltration Over Command and Control Channel). - The compromised data set includes student identification numbers, personal email addresses and message content exchanged between teachers, professors and students. Passwords, dates of birth, government IDs and financial information were not found in the leaked material. - Affected entities span K‑12 districts, community colleges and major universities, including Charlottesville City Schools, Greene County Public Schools and UVA. Central Virginia schools are conducting separate investigations to determine local impact. - The breach was discovered when administrators noticed anomalous login activity dating back to April 25. Instructure confirmed the platform remains operational and has not observed service disruption.
What It Means Exposed contact information enables targeted spear‑phishing campaigns, where attackers craft messages that appear to come from teachers or classmates. Graham emphasized that recipients should scrutinize any unexpected links or attachments, even if the sender’s name is familiar. The incident underscores the growing risk of supply‑chain attacks on shared SaaS (Software‑as‑a‑Service) platforms used by education.
Mitigations - Enforce multi‑factor authentication (MFA) for all Canvas users; MFA adds a second verification step, dramatically reducing the value of stolen credentials. - Rotate passwords for all Canvas accounts and require complex, unique passwords. - Deploy email filtering solutions that detect suspicious sender domains and known phishing patterns. - Monitor login anomalies using UEBA (User and Entity Behavior Analytics) to flag impossible travel or logins from unfamiliar IP ranges. - Apply the latest security patches from Instructure and review API permissions to ensure only necessary scopes are granted. - Conduct regular phishing simulations and security awareness training for students and staff.
Looking Ahead Security teams should watch for follow‑up activity from the Shiny Hunters group, including potential credential‑stuffing attacks on other education platforms. Continuous monitoring and rapid MFA adoption will be critical to limiting further exposure.
Continue reading
More in this thread
Conversation
Reader notes
Loading comments...