World Password Day 2026 Shows One‑Third Still Write Down Passwords, 20% Reuse Them
Survey shows 35% write passwords down and 19% reuse them, fueling massive breach compilations. Learn mitigations and future trends.
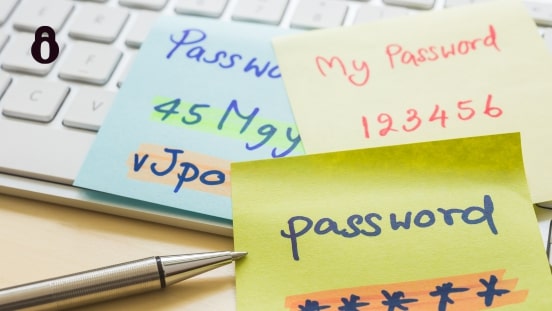
*TL;DR: Over a third of people still write passwords down and almost one‑fifth reuse the same password across accounts, keeping billions of credentials vulnerable in massive breach compilations.
Context World Password Day 2026 highlights a gap between advice and practice. Despite widespread guidance to use unique, long passwords and enable two‑factor authentication, convenience drives risky habits.
Key Facts - The Bitdefender Consumer Cybersecurity Survey 2025 reports 35% of respondents write passwords on paper, a sticky note, or a digital file. - 19% admit to reusing the same password on multiple services, increasing the chance that a single breach compromises many accounts. - The “Mother of All Breaches” aggregated roughly 1.2 TB of login data, exposing billions of email addresses, usernames, and passwords. The dataset continues to circulate on underground forums. - Credential‑stealing malware such as LummaStealer spreads via fake download links and phishing pages, harvesting saved passwords, autofill data, and session cookies. - Password reuse amplifies impact: a compromised email often unlocks password‑reset links for banking, social media, and corporate accounts.
What It Means Writing passwords down creates a physical attack surface; a lost notebook can hand an attacker a master key. Reuse turns a single leaked password into a pivot point for lateral movement across personal and professional services. The persistence of massive breach compilations means that old credentials remain weaponized for years, feeding automated credential‑stuffing attacks that test billions of login combos against vulnerable sites.
Mitigations - Deploy a reputable password manager to generate and store unique, high‑entropy passwords for every account. This eliminates the need for handwritten notes and reduces reuse. - Enable multi‑factor authentication (MFA) wherever possible; a one‑time code or hardware token adds a barrier even if a password is exposed. - Regularly audit stored credentials against known breach data using services that reference CVE‑2021‑44228 (Log4j) style disclosures and the MITRE ATT&CK technique T1110 (Brute Force). Replace any matching passwords immediately. - Educate users on phishing detection and restrict execution of unknown binaries to curb infostealer infection vectors. - For organizations, enforce password policies that require minimum length, complexity, and periodic rotation, and monitor authentication logs for anomalous login attempts indicative of credential‑stuffing.
Looking Ahead Watch for broader adoption of password‑less authentication methods such as WebAuthn passkeys, which could shrink the attack surface that current password habits sustain.
Continue reading
More in this thread
SEBI Flags AI‑Powered Vulnerability Scanners as Emerging Cyber Threat
Peter Olaleru
SEBI Flags AI Vulnerability Tools as New Cyber Risk, Launches Task Force
Peter Olaleru
Over a Third Write Down Passwords, Nearly 20% Reuse Them Despite World Password Day Alerts
Peter Olaleru
Conversation
Reader notes
Loading comments...