Vercel Database Leak Sold for $2 Million After Context AI Supply‑Chain Breach
Vercel’s internal database was leaked and sold for $2 million after a supply‑chain attack via Context AI. Learn the timeline, impact, and immediate mitigation steps.
Vercel Database Leak Sold for $2 Million After Context AI Supply‑Chain Breach
TL;DR
On April 19, 2026, Vercel’s internal user database appeared for sale on BreachForums for $2 million after a supply‑chain breach via Context AI.
Context
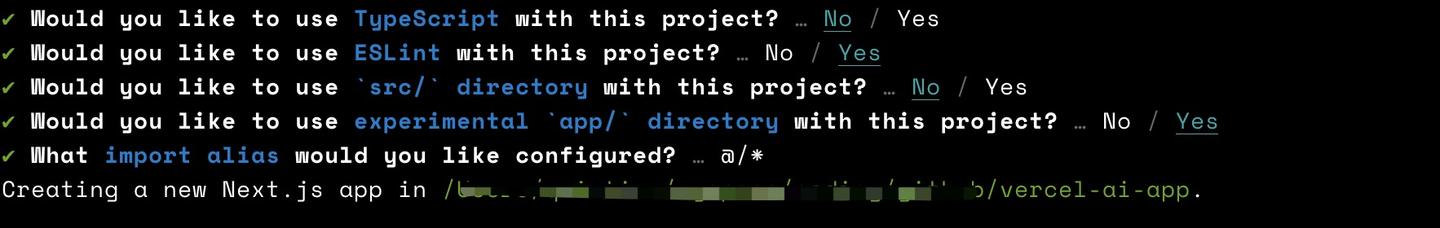
Vercel provides a platform for hosting and scaling web applications. Context AI offers AI‑powered browser extensions. On April 19, Vercel disclosed that its environment was compromised through a third‑party breach at Context AI. The attack chain began when a Context AI employee’s device was infected after downloading game exploits, exposing Google Workspace credentials and OAuth tokens.
Key Facts
A Vercel employee used his Vercel Enterprise Google account to grant Context AI full read access to his Google Drive. The compromised Context AI Chrome extension, identified by ID omddlmnhcofjbnbflmjginpjjblphbgk, served as the indicator of compromise. Threat actors later posted Vercel’s internal database on BreachForums, asking $2 million for the data.
What It Means
The leaked database likely contains user records, API keys, GitHub tokens, and npm package maintainer credentials. Exposure of these secrets could enable further supply‑chain attacks on popular Vercel‑maintained projects such as Next.js, Turbopack, and the AI SDK. While Vercel stated its core software remained safe, the breach highlights the risk of excessive OAuth scopes and unencrypted environment variables.
Mitigations
- Rotate all API keys, GitHub tokens, and npm credentials associated with Vercel and Context AI accounts. - Enforce multi‑factor authentication on Google Workspace and developer accounts. - Audit Google OAuth third‑party apps; revoke access for app ID 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com and remove the Context AI extension (ID omddlmnhcofjbnbflmjginpjjblphbgk). - Pin Vercel‑maintained npm packages to specific versions and monitor for unexpected updates. - Deploy detection rules for the known Chrome extension ID and for anomalous OAuth token usage (MITRE ATT&CK T1078, T1133).
Watch for any misuse of the leaked data on underground forums and for further advisories regarding Vercel‑maintained packages.
Continue reading
More in this thread
Seiko USA Faces 72‑Hour Ransom Threat After Hackers Claim Shopify Breach and Customer Data Theft
Peter Olaleru
Elmwood Healthcare Breach Exposes SSNs and Medical Data, Triggering Class Action Investigation
Peter Olaleru
Elmwood Healthcare Breach Exposes SSNs and Medical Data, Prompting Class‑Action Inquiry
Peter Olaleru
Conversation
Reader notes
Loading comments...