Vercel Breach Traced to Context AI OAuth Exploit, Warns of Hundreds Affected
Vercel confirms a security breach impacting internal systems and customer data via a Context AI OAuth exploit. Learn how hundreds of organizations are affected and what steps to take.
**TL;DR** Vercel, a leading cloud development platform, confirmed a security breach that compromised internal systems and potentially hundreds of customer organizations. An OAuth exploit involving a third-party AI application facilitated the attack.
**Context** Vercel disclosed the breach after an employee installed a Context AI application, which attackers leveraged. This incident underscores the increasing threat of supply chain attacks through seemingly innocuous third-party integrations. Hackers claimed to have stolen sensitive customer credentials from Vercel’s systems and offered them for sale online.
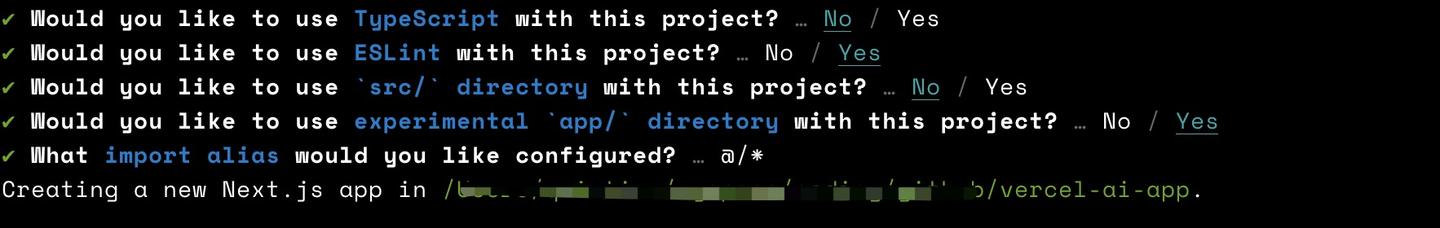
**Key Facts** The breach initiated when a Vercel employee integrated a Context AI app. This integration allowed attackers to hijack the employee’s Google account via an OAuth exploit. OAuth (Open Authorization) is a standard allowing applications to access user data on other services without sharing direct passwords, often requiring user consent for specific permissions. With control of the Google account, attackers gained unauthorized access to Vercel's internal systems, including unencrypted credentials. Vercel issued a warning that the breach’s reach extends beyond its immediate infrastructure, potentially affecting hundreds of users across numerous organizations utilizing its platform. While a threat actor claiming to represent the ShinyHunters group advertised the stolen data, the group later denied any involvement in this specific incident. Context AI had previously reported a breach in March concerning its consumer app, which may be connected to this larger event.
**What Defenders Should Do** All organizations leveraging Vercel should immediately audit and rotate all active API keys and credentials, prioritizing those in "non-sensitive" deployments as recommended by Vercel's CEO. Implementing strong multi-factor authentication (MFA) for all employee and administrative accounts is crucial to prevent account takeovers. Security teams must review and restrict third-party application permissions, especially those granted via OAuth, adhering strictly to the principle of least privilege. Regular security awareness training for employees should emphasize the risks of unauthorized application installations and the potential for credential exposure. Furthermore, encrypting all sensitive internal credentials, both at rest and in transit, significantly reduces the impact of such breaches.
**What to Watch Next** As Vercel continues its investigation and seeks more information from Context AI, the full scope of compromised data and the ultimate downstream impact on affected organizations will become clearer. This incident highlights the need for continuous vigilance regarding third-party software supply chain security.
Conversation
Reader notes
Loading comments...