Vercel Breach Traced to Compromised Third-Party AI Tool, Exposes 580 Employee Records
Vercel confirms a breach exposing 580 employee records, linked to a compromised third-party AI tool and an employee's Google Workspace account takeover.
A Vercel security breach exposed 580 employee records, originating from a compromised third-party AI tool that provided access to an employee's Google Workspace account.
Cloud platform Vercel recently confirmed attackers breached its internal systems, affecting a limited subset of customers. The incident exposed non-sensitive environment variables, which are configuration settings used by software applications. The company reported that its core services remained operational, and it has since contacted affected users, advising them to rotate credentials.
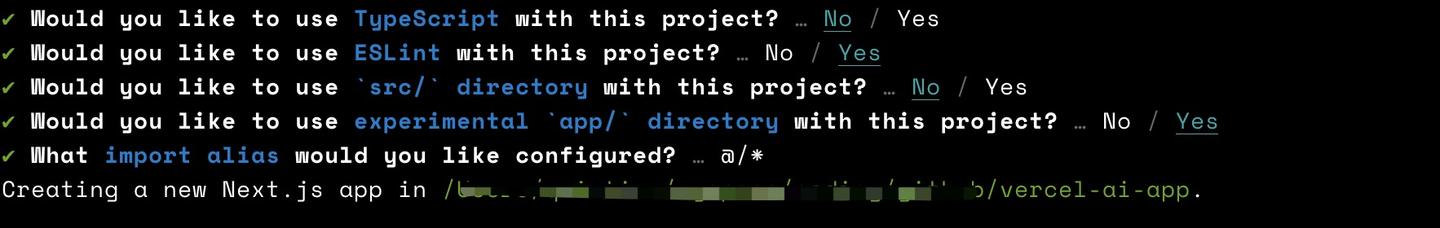
The attack initiated through Context.ai, a third-party AI tool. Attackers exploited a vulnerability in Context.ai's now-deprecated AI Office Suite, gaining unauthorized access to its AWS environment. This compromise led to the theft of an OAuth token, a digital key that grants limited, temporary access to a user's account on one service from another without needing a password. Attackers then used this compromised OAuth token to take over a Vercel employee's Google Workspace account.
Following the Google Workspace account takeover, the attackers escalated their access within Vercel environments. This allowed them to view additional environment variables, which Vercel had not designated as sensitive. A threat actor later allegedly shared a dataset containing approximately 580 Vercel employee records on a hacking forum. While claims of further data exfiltration, including source code and database contents, circulated, Vercel stated it found no evidence of unauthorized access to sensitive variables.
### Mitigations
This incident underscores the critical risks associated with supply chain attacks, where a compromise in one vendor can cascade across interconnected systems. Organizations should implement robust third-party risk management programs. Regularly auditing permissions granted to third-party applications, especially those using OAuth tokens, is essential. Strong multi-factor authentication (MFA) must be enforced across all corporate accounts, particularly those integrated with external services like Google Workspace. Companies should also classify all environment variables by sensitivity and restrict access based on the principle of least privilege. Regular credential rotation and continuous monitoring for unusual account activity are further critical defensive measures.
Watch for evolving disclosures regarding the full scope of data impact and any further details on the threat actor's identity or tactics.
Continue reading
More in this thread
English Council Data Breaches Jump 53% in Five Years, Wiltshire Leads with 601% Spike
Peter Olaleru
AES-128 Stands Strong Against Quantum Threats, Expert Debunks Grover’s Algorithm Myths
Peter Olaleru
English council data breaches jump 53% in five years, with Wiltshire seeing a 601% surge
Peter Olaleru
Conversation
Reader notes
Loading comments...