Vercel Breach Traced to Roblox Cheat Malware, CEO Warns AI‑Accelerated Attackers
Vercel's security incident began with Roblox cheat malware, compromising an employee account. CEO warns of sophisticated, AI-accelerated attackers.
TL;DR
A sophisticated cyberattack on Vercel began with a third-party employee's system infected by Roblox cheat malware, leading to a Vercel account compromise and internal data access. The CEO indicates the attackers likely utilized AI for their swift, targeted operations.
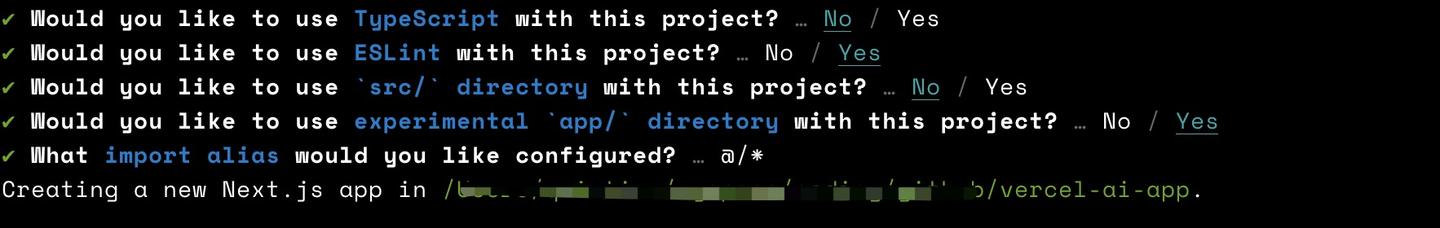
The Vercel security incident stems from a malware infection on a third-party employee's device, not Vercel's own systems. An employee, reportedly searching for Roblox game exploits, downloaded Lumma Stealer malware. This malware compromised their system, ultimately yielding an OAuth token for a Vercel employee's Google Workspace account.
Attackers then used the compromised Vercel employee’s Google Workspace account to access Vercel environments. This initial access exposed non-sensitive environment variables, which the attackers reportedly leveraged through enumeration to gain deeper understanding of internal systems.
Vercel’s CEO states the attackers are highly sophisticated and potentially accelerated by artificial intelligence, moving with surprising speed and demonstrating deep knowledge of Vercel's infrastructure. The threat group ShinyHunters has claimed responsibility for the breach, attempting to sell what they assert are stolen access keys, source code, and databases.
While Vercel indicated only a limited number of customers were impacted and advised credential rotation, the attack highlights critical vulnerabilities in interconnected cloud services. The incident showcases how a compromise outside an organization can cascade through third-party application permissions to impact internal systems.
### What Defenders Should Do
Organizations must enforce stringent security hygiene, starting with strong multi-factor authentication (MFA) across all accounts, especially those accessing critical business environments. Regularly review and revoke third-party application permissions to ensure they adhere to the principle of least privilege, minimizing potential lateral movement for attackers. Promptly rotate credentials, API keys, and environment variables when any associated account or service shows signs of compromise. Monitor for suspicious activity, particularly anomalous logins and data access patterns, and establish robust endpoint detection and response (EDR) solutions. Investigations into the Vercel breach, aided by CrowdStrike and Mandiant, remain ongoing; watch for further indicators of compromise and mitigation advisories from Vercel.
Continue reading
More in this thread
DeepMind Warns of AI Agent Traps Hidden in Web Pages That Can Hijack Autonomous Agents
Peter Olaleru
Endue Settlement: $2,500 Cash, Free ID Monitoring
Peter Olaleru
Endue Software Settlement Offers Up to $2,500 Cash and Free Medical Identity Monitoring
Peter Olaleru
Conversation
Reader notes
Loading comments...