Vercel Breach Traced to Roblox Cheat Malware, CEO Warns AI‑Accelerated Attackers
A cybersecurity breach at Vercel began with Roblox cheat malware infecting a Context.ai employee, leading to stolen credentials. Vercel CEO warns of AI-accelerated attackers.
TL;DR
The Vercel security breach originated from a third-party compromise involving Roblox cheat malware, exposing customer credentials and internal data. Vercel's CEO suggests the attackers employed advanced, potentially AI-accelerated tactics, prompting urgent calls for credential rotation.
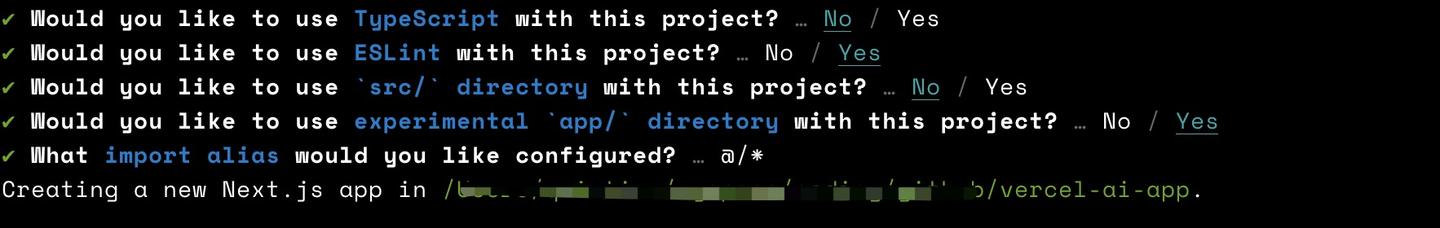
A cybersecurity incident at cloud platform Vercel began with an employee's personal computer compromise outside Vercel's direct network. An infostealer, specifically Lumma Stealer malware, was the initial vector, designed to pilfer credentials and sensitive information. This malware infected a Context.ai employee's system after they sought Roblox game exploits, a common tactic for distributing such threats.
The attack started in February when Lumma Stealer malware infected a Context.ai employee's machine. This granted attackers access to Context.ai’s Amazon Web Services (AWS) environment and OAuth tokens—digital keys for accessing online services. Attackers then exploited an OAuth token linked to a Vercel employee's Google Workspace account, which had been granted full access to Context AI Office Suite. This enabled them to infiltrate some Vercel environments and access certain environment variables, which are dynamic values that control program behavior.
The group ShinyHunters claimed responsibility, attempting to sell Vercel access keys, source code, and databases. While Vercel states its customer data is encrypted, a limited number of customers received advisories to rotate their credentials. The initial compromise of Context.ai's OAuth app may impact hundreds of users across multiple organizations. Vercel CEO Guillermo Rauch noted the attackers displayed "surprising velocity" and "in-depth understanding of Vercel," strongly suspecting their operations were "significantly accelerated by AI."
This incident highlights the interconnected risks of cloud services and third-party integrations. A single point of failure, even on a personal device, can cascade into a broader organizational compromise. The use of common malware combined with sophisticated lateral movement underscores the blend of accessible tools and advanced techniques in modern attacks. The CEO’s comments about AI acceleration point to a future where threat actors leverage automated processes for reconnaissance and exploitation, increasing attack speed and precision.
### Mitigations
Organizations must enforce strong multi-factor authentication (MFA) across all accounts, especially for cloud and SaaS applications. Regularly review and revoke OAuth token permissions, ensuring only necessary access is granted to third-party services. Implement endpoint detection and response (EDR) solutions to identify and block infostealer malware like Lumma Stealer. Conduct security awareness training, emphasizing the risks of downloading unverified software, even for personal use on work-provisioned devices. Vercel has released indicators of compromise (IoCs); customers should review their activity logs for suspicious entries and immediately rotate all sensitive environment variables and API keys.
The ongoing investigations by Vercel, Context.ai, CrowdStrike, and Mandiant will likely reveal further insights into these evolving, AI-enhanced attack methodologies.
Continue reading
More in this thread
Conversation
Reader notes
Loading comments...