Vercel Breach Traced to Compromised Context.ai OAuth App, Exposes Limited Customer Credentials
Vercel confirmed a data breach stemming from a compromised Context.ai OAuth app, leading to exposure of limited customer credentials. Learn the details and mitigation steps.
Cloud platform Vercel recently confirmed a data breach originating from a compromised Google Workspace OAuth application used by a Vercel employee, leading to unauthorized access to internal infrastructure. This incident exposed credentials for a limited number of customers, who have since been notified to rotate their secrets.
### The Breach's Origin Vercel, a leading cloud platform provider, recently confirmed unauthorized access to its internal infrastructure. The attack vector was identified as a compromised Google Workspace OAuth (Open Authorization) application tied to Context.ai, an artificial intelligence tool used by a Vercel employee. OAuth is an authentication standard that allows third-party applications to access user data without sharing direct login credentials.
Attackers exploited this vulnerability to hijack the employee’s Google Workspace account, subsequently gaining entry into Vercel’s corporate network. This method of compromise highlights the growing threat from supply chain attacks, where adversaries target less-secured third-party services to access a primary objective.
### Scope and Impact Once inside, the unauthorized access allowed threat actors to read specific environment variables within certain Vercel environments. Environment variables are small key-value pairs that store configuration settings, API keys, and other secrets necessary for an application to function. Critically, only those variables *not* explicitly marked as "sensitive" by Vercel's internal protections were accessed.
Vercel confirmed that a limited number of customers had their credentials compromised as a result of this access. The company has directly contacted all affected users, mandating immediate credential rotation. Vercel emphasizes that there is no evidence to suggest that properly tagged sensitive environment variables were accessed or exfiltrated, and all Vercel services remain fully operational. The company is actively collaborating with incident response experts like Mandiant and law enforcement in its ongoing investigation.
### Mitigation and Defense Organizations using Google Workspace, particularly those integrating third-party AI tools, should immediately audit OAuth application access. Specifically, administrators must disable the malicious Context.ai OAuth App ID: `110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com`. This step is crucial for preventing similar compromises across other potentially affected organizations.
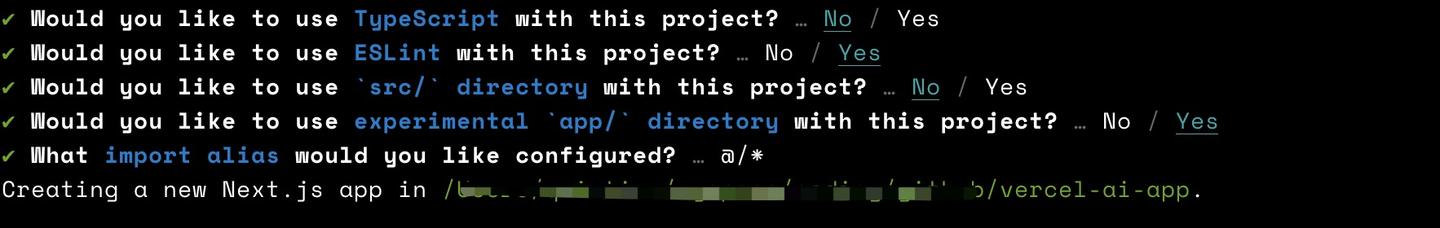
Vercel customers must take proactive measures: review activity logs in their dashboard or command-line interface for any suspicious actions. Immediately rotate any environment variables containing secrets like API keys or database credentials if they were not marked as sensitive prior to the incident. Moving forward, enable the sensitive environment variables feature for all secret values.
Further actions include auditing recent deployments for unexpected changes and ensuring Deployment Protection settings are configured to "Standard" at a minimum, with associated deployment tokens rotated. This incident underscores the ongoing challenge of securing interconnected digital ecosystems. Businesses must intensify efforts to audit third-party integrations and enforce strict privilege management across all employee-used applications to mitigate similar risks.
Conversation
Reader notes
Loading comments...