Vercel Breach Linked to Context.ai Compromise, ShinyHunters Claims $2M Data Sale
Vercel discloses a security breach originating from a compromised Context.ai tool, leading to limited customer credential exposure. ShinyHunters claims responsibility, asking $2M for data.
**TL;DR** Vercel confirmed a security breach originating from a compromised third-party AI tool, Context.ai. Threat actor ShinyHunters claims responsibility, offering stolen data for $2 million and impacting a limited number of Vercel customer credentials.
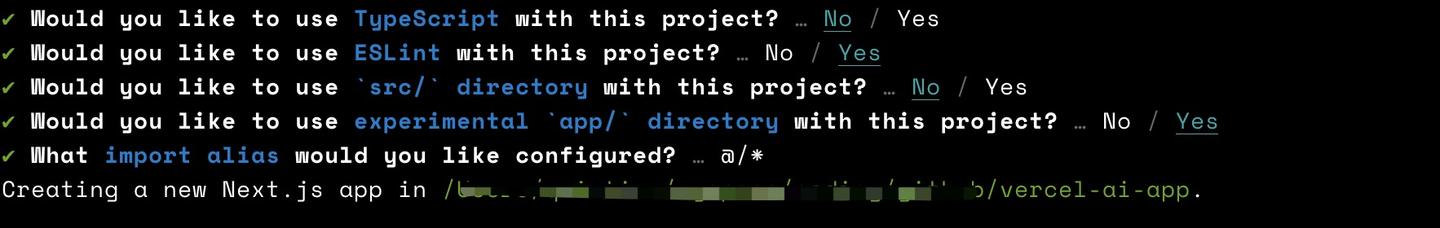
Vercel, a prominent web infrastructure provider, recently disclosed a security breach granting unauthorized access to certain internal systems. The incident originated from the compromise of Context.ai, a third-party artificial intelligence (AI) tool utilized by a Vercel employee. Attackers leveraged this initial access to gain control of the employee's Vercel Google Workspace account.
This compromise enabled access to specific Vercel environments and environment variables not designated as "sensitive." Environment variables are key-value pairs that store configuration settings for applications. Vercel stated that any variables marked sensitive are encrypted and found no evidence of their access. The company describes the threat actor as sophisticated, citing their operational velocity and deep understanding of Vercel's systems.
A limited subset of Vercel customers had their credentials compromised during the incident. Vercel is directly contacting these affected customers, urging them to rotate their credentials immediately. Concurrently, a threat actor operating under the alias ShinyHunters has claimed responsibility for the breach and is offering the allegedly stolen data for $2 million. Vercel is actively collaborating with Google-owned Mandiant, other cybersecurity firms, and law enforcement, while engaging with Context.ai to understand the full scope of the breach.
Organizations must prioritize robust security practices to counter evolving supply chain attacks. Google Workspace administrators and account owners should inspect for a suspicious OAuth application with the ID `110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com`. Defenders should also review activity logs for unusual behavior and audit all environment variables, ensuring sensitive secrets are always stored using encryption mechanisms or dedicated sensitive variable features. Furthermore, investigate recent deployments for any unexpected changes and confirm that Deployment Protection is set to Standard as a minimum, rotating any associated tokens. Vercel has already rolled out new dashboard capabilities to enhance environment variable management and security for its users.
The incident highlights the critical need for vigilance over third-party integrations and internal credential hygiene. Organizations must continue to scrutinize third-party tool access and enforce strict credential management to mitigate similar supply chain risks.
Conversation
Reader notes
Loading comments...