Shiny Hunters Claims 275 Million Records Stolen in Canvas Breach During Finals
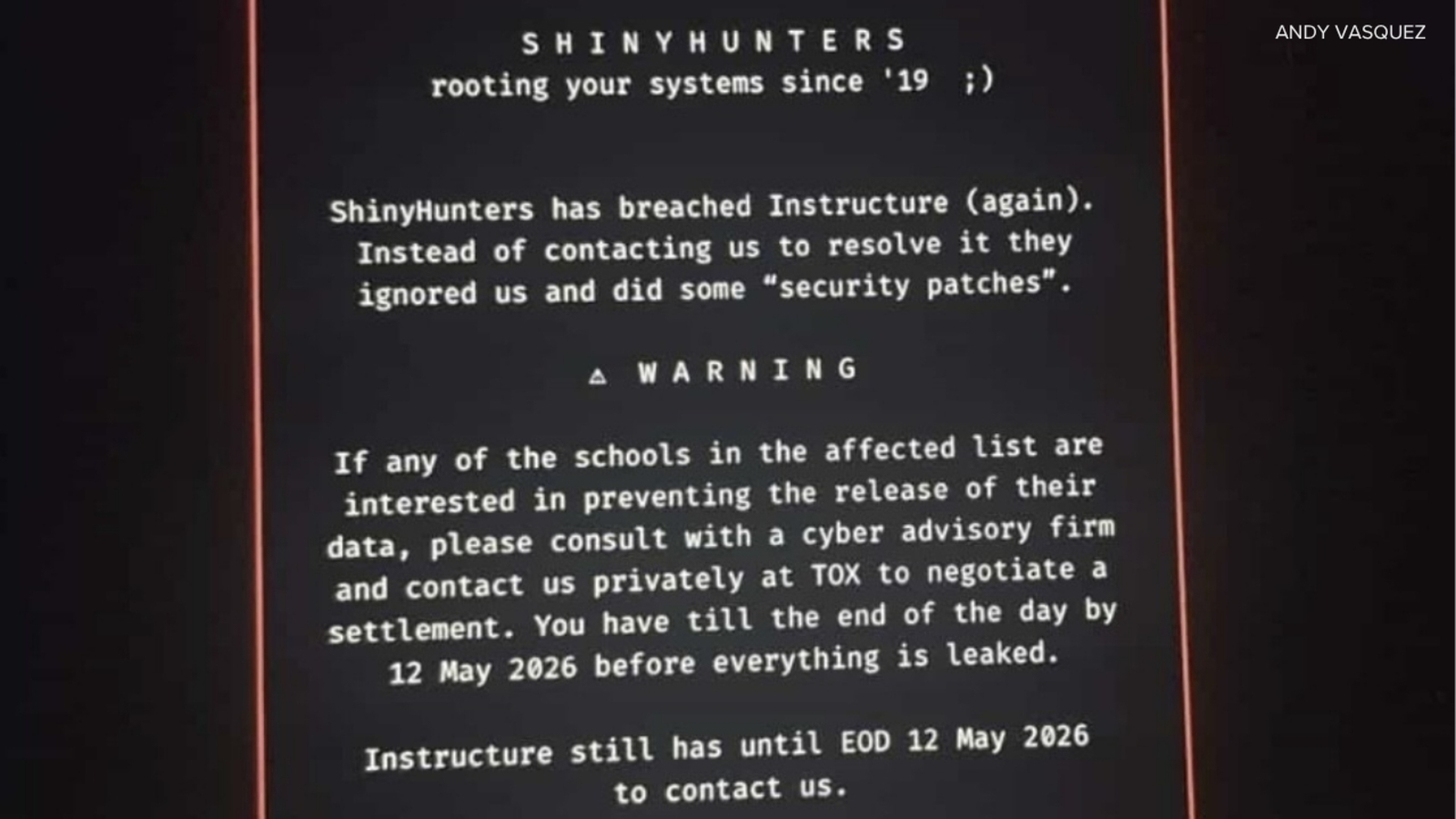
Extortion group Shiny Hunters says it exfiltrated 275 million education records from Canvas, disrupting finals week for thousands of students.
TL;DR
– Extortion gang Shiny Hunters says it stole more than 275 million Canvas records, crippling coursework for students during finals.
Context Instructure, the vendor behind Canvas, announced a “cybersecurity incident” early Thursday. The learning‑management system—used by universities, community colleges and K‑12 districts—went into maintenance mode, leaving grades, assignments and communications inaccessible. The outage hit institutions across the United States, including several California State University campuses, just as semester‑end assessments began.
Key Facts - The threat actor identified as Shiny Hunters publicly claimed responsibility. Their statement alleges the exfiltration of 275 million records belonging to students, teachers and staff worldwide. - The group threatened to publish billions of private messages unless a ransom is paid by May 12. - CSU Northridge student Alfonso Vargas described the timing as “the worst possible time” because finals are underway and instructors are still setting deadlines. - Glendale Community College announced a shift to alternative platforms and cited existing backups as a mitigation measure, though such redundancy is not universal. - Instructure’s initial notice did not disclose the attack vector, but early analysis points to compromised credentials used to access the Canvas API (Application Programming Interface). The technique aligns with MITRE ATT&CK T1078 — Valid Accounts, often paired with T1059 — Command‑Line Interface for lateral movement. - No CVE (Common Vulnerabilities and Exposures) has been linked to the breach, suggesting the compromise stemmed from credential theft rather than a software flaw.
What It Means The scale of the data set—275 million records—makes this one of the largest education‑sector breaches on record. Exposed data likely includes names, email addresses, enrollment numbers and possibly hashed passwords. If the stolen credentials are reused on other services, attackers could pivot to additional institutional systems. The threat of publicizing private communications adds pressure on schools to meet the ransom deadline, but paying does not guarantee data deletion.
Mitigations – What Defenders Should Do 1. Reset all Canvas credentials and enforce multi‑factor authentication (MFA) for every user. MFA blocks unauthorized logins even if passwords are compromised. 2. Audit API keys for unused or over‑privileged tokens; revoke any that are not essential. Limit API access to least‑privilege scopes. 3. Deploy detection signatures for suspicious login patterns, such as logins from atypical geolocations or rapid credential use across multiple accounts (ATT&CK T1110 — Brute Force). 4. Validate backups and test restoration procedures. Institutions without recent backups should prioritize creating immutable snapshots stored offline. 5. Monitor for data‑leak indicators on underground forums and paste sites. Early detection of leaked files can trigger incident response and legal actions. 6. Review and update incident‑response playbooks to include extortion scenarios, ensuring legal counsel and communications teams are engaged promptly.
The breach underscores the need for robust identity hygiene and backup strategies in education technology. Watch for further disclosures from Instructure and law‑enforcement on the ransom demand and any additional threat‑actor tactics.
Continue reading
More in this thread
Conversation
Reader notes
Loading comments...