Pitney Bowes Confirms Salesforce Breach After Phishing, ShinyHunters Claims 25M Records Leaked
Details on the Pitney Bowes Salesforce breach: phishing vector, timeline, data scope, and defender actions.
TL;DR
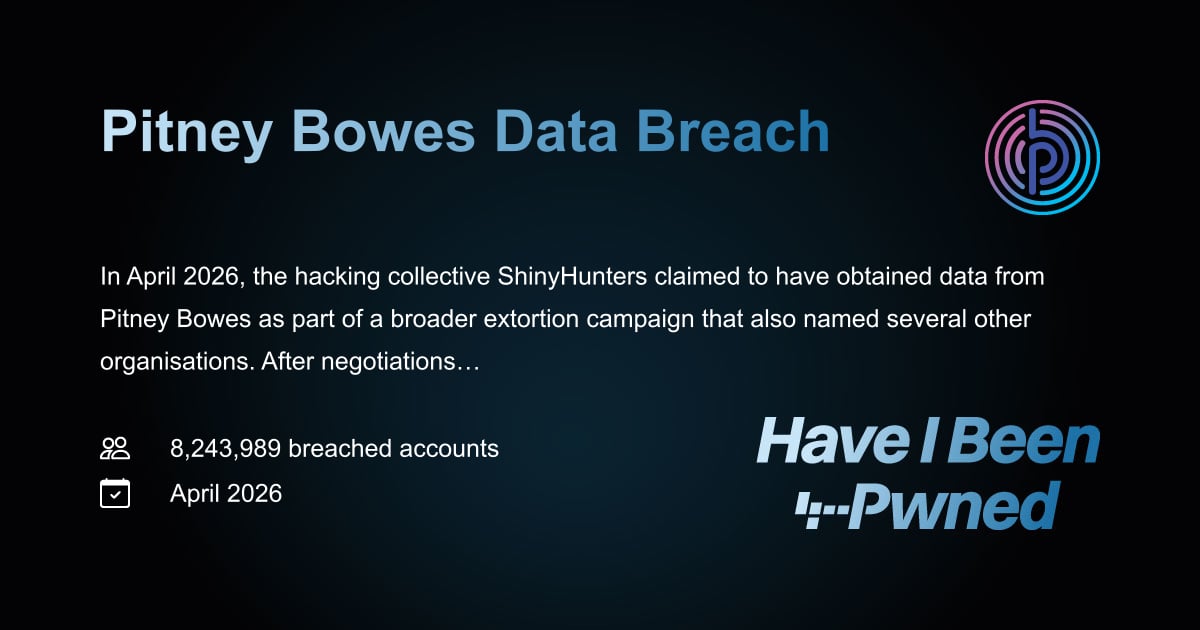
On April 9 Pitney Bowes detected unauthorized Salesforce access stemming from a phishing‑compromised employee email; Have I Been Pwned later confirmed 8.2 million unique email addresses in the leaked data, while the ShinyHunters group claims over 25 million records were exfiltrated.
Context Pitney Bowes, a U.S. provider of shipping, mailing, and financial‑services software, disclosed that the intrusion was limited to its Salesforce CRM environment. The company said it revoked the compromised credentials, engaged external investigators, and notified affected business customers. It maintains that no sensitive personal data was accessed, though the leaked dataset includes business contact information.
Key Facts The attack began with a phishing email that stole an employee’s login details, a classic T1566.001 (Spearphishing Attachment) technique. Using those valid credentials (T1078), the threat actor accessed Salesforce, likely via the web UI or API, and extracted customer account and contact records. Have I Been Pwned’s addition of the leak shows 8.2 million unique email addresses, about half of which were new to the service. ShinyHunters, known for extorting SaaS platforms, posted the data on its portal after ransom talks failed and claims the total exceeds 25 million records.
What It Means For defenders, the incident underscores the need to protect cloud‑service credentials against phishing. Recommended steps include: enforce phishing‑resistant MFA (e.g., FIDO2 or push‑based approvals), enable Salesforce login IP restrictions and session monitoring, review OAuth token usage, and rotate any potentially compromised service accounts. Implement detection for anomalous login patterns (MITRE ATT&CK T1078.003) and unusual data export volumes (T1041). Audit logs should be retained for at least 90 days and reviewed for privilege escalation attempts (T1068).
Watch for any resale of the leaked data on underground markets, further extortion attempts from ShinyHunters, and potential regulatory inquiries regarding the handling of business‑contact data under GDPR or CCPA.
Continue reading
More in this thread
Conversation
Reader notes
Loading comments...