Carnival Faces 7.5 Million Email Leak Claim Amid ShinyHunters Extortion Dispute
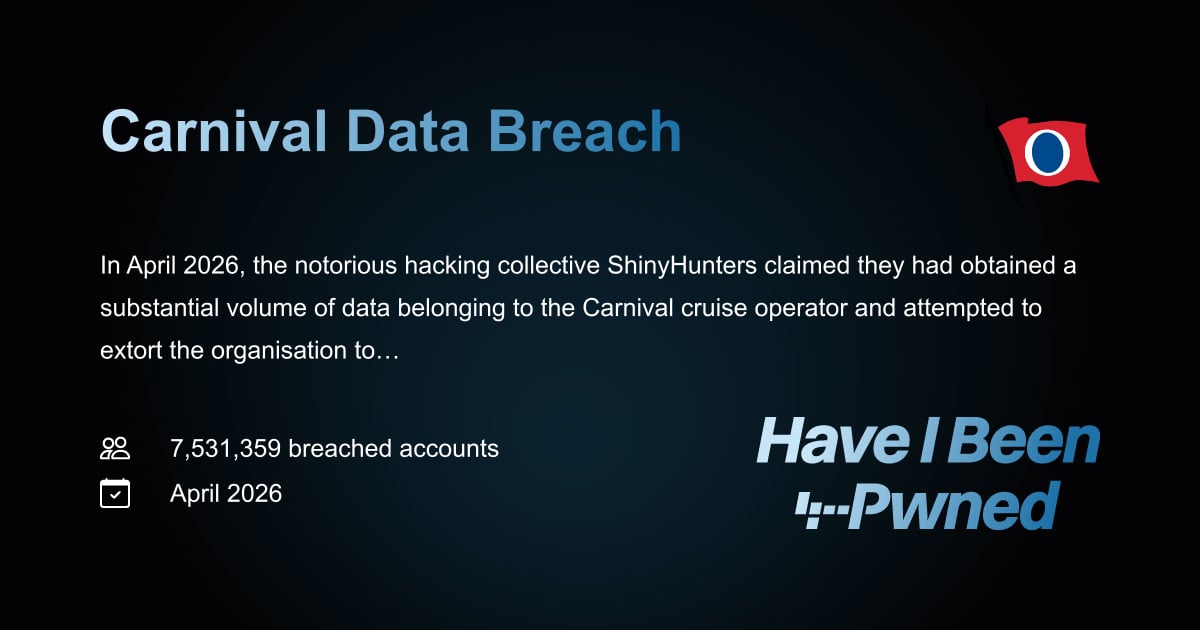
Have I Been Pwned reports 7.5 million unique emails from Carnival’s loyalty program exposed; ShinyHunters claims larger data theft after failed talks.
Carnival Faces 7.5 Million Email Leak Claim Amid ShinyHunters Extortion Dispute
TL;DR
Have I Been Pwned flagged 7.5 million unique email addresses tied to Carnival’s Mariner Society loyalty program, while ShinyHunters asserts it stole far more data after extortion talks collapsed. Carnival says the incident stemmed from a phishing attack on a single user account.
Context The exposed data includes names, dates of birth, genders, and membership status for the Mariner Society program operated by Holland America Line, a Carnival subsidiary. Have I Been Pwned notes the haul totals 8.7 million records, suggesting additional fields beyond email addresses. ShinyHunters posted on its leak site that Carnival failed to reach an agreement despite their patience and accused the company of not caring.
Key Facts ShinyHunters claims it obtained not only the loyalty data but also terabytes of internal corporate data after negotiations broke down. Carnival acknowledges a security incident but limits its description to a phishing compromise of a single user account, stating it is still assessing the scope of any unauthorized access. The group is known for using phishing, stolen credentials, or SaaS platform intrusions to gain initial footholds, aligning with MITRE ATT&CK technique T1566 (Phishing).
What It Means If ShinyHunters’ claim of broader data theft is accurate, the incident could expose internal communications, financial records, or operational details, increasing risk of follow‑on fraud or secondary attacks. Even the confirmed email leak enables credential stuffing and targeted phishing against loyalty program members. Organizations should treat the event as a reminder that a single compromised credential can cascade into larger data exposure.
What Defenders Should Do - Enforce multi‑factor authentication on all user accounts, especially those with access to loyalty or customer databases. - Deploy anti‑phishing controls such as URL rewriting and attachment sandboxing; monitor for T1566.001 (Spearphishing Attachment) and T1566.002 (Spearphishing Link). - Review and restrict privileged access to SaaS platforms using least‑privilege principles and regular access‑rights audits. - Implement detection rules for unusual data exfiltration volumes (e.g., large outbound transfers to unfamiliar IP ranges) and for anomalous login patterns from compromised credentials. - Ensure patch management covers known vulnerabilities in web‑facing applications; consult vendor advisories for any CVEs related to the exploited services.
Watch for any appearance of the alleged internal data on underground markets and for Carnival’s forthcoming forensic report detailing the true scope of the breach.
Continue reading
More in this thread
UK NCSC Advises Public to Replace Passwords with Passkeys as Adoption Grows
Peter Olaleru
Aptica Releases SMB Cybersecurity Guide Amid 88% Ransomware Share in Small Business Breaches
Peter Olaleru
ShinyHunters Claims Massive Carnival Data Leak While Company Cites Single‑User Phishing
Peter Olaleru
Conversation
Reader notes
Loading comments...